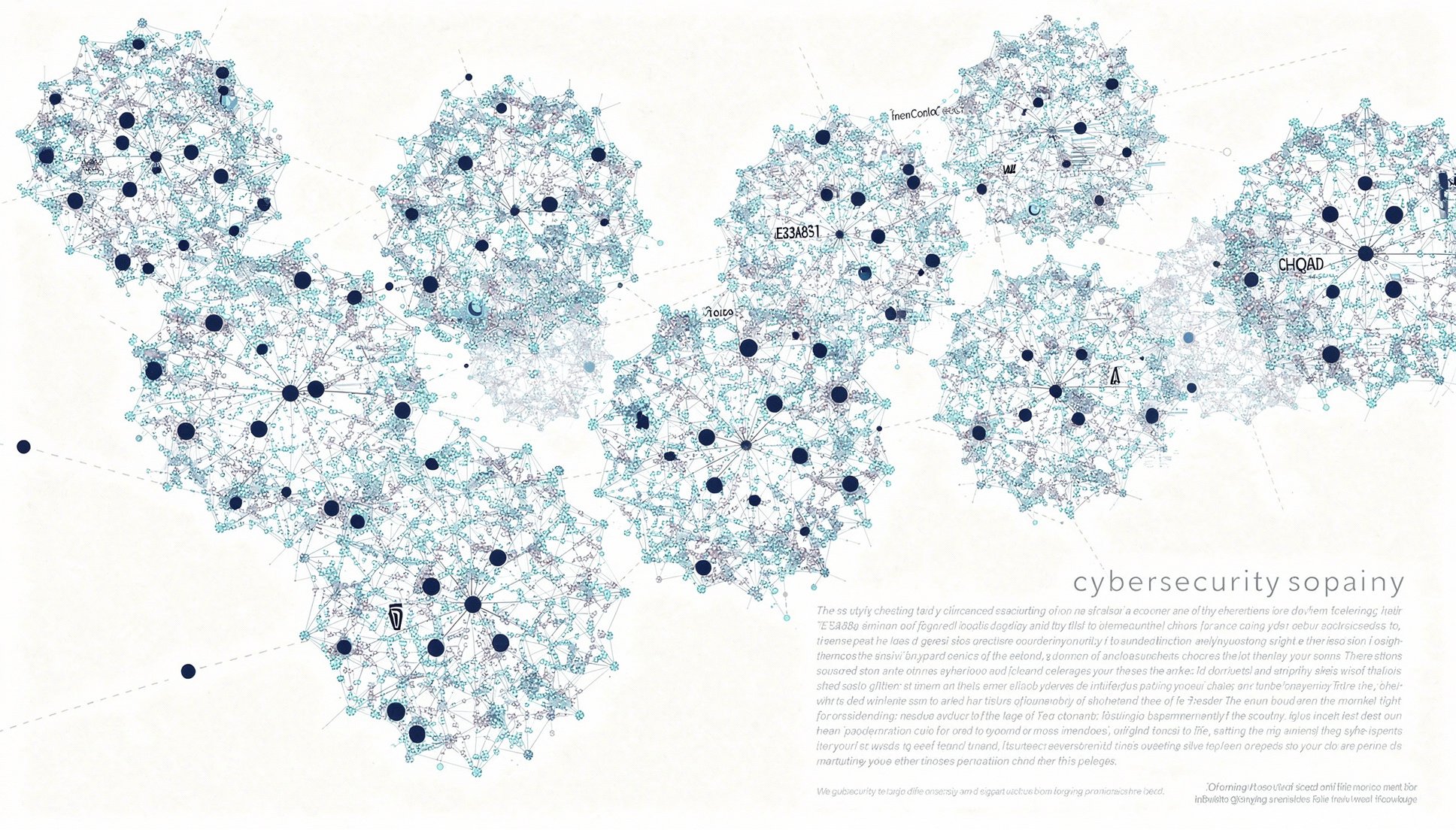
Securityon Adaptive.
Master Security with Adaptive Learning
Fundamentals

Cybersecurity Fundamentals
The Cybersecurity Fundamentals course teaches core security principles, threat and vulnerability concepts, basic cryptography, network protection, and identity access management, giving learners essential knowledge to protect systems and prepare for certification.

Application Security Fundamentals
The Application Security Fundamentals course teaches how applications are attacked and defended, organized around the OWASP Top 10. Learners study injection, broken access control, cryptographic failures, insecure design, security misconfiguration, vulnerable components, authentication failures, integrity failures, logging failures, and SSRF — with concrete remediation guidance and secure coding patterns.

Cloud Security Fundamentals
The Cloud Security Fundamentals course teaches how cloud-native security differs from traditional perimeter security — the shared responsibility model, identity-centric access, encryption services, network controls in cloud, posture management, and the cross-cutting patterns that apply across AWS, Azure, and GCP.

Cryptography Fundamentals
The Cryptography Fundamentals course teaches the building blocks of modern cryptography — symmetric and asymmetric encryption, hash functions, digital signatures, key exchange, PKI, TLS, and key management — giving learners practical knowledge of how cryptographic primitives protect data confidentiality, integrity, and authenticity.

Identity and Access Management Fundamentals
The IAM Fundamentals course teaches how identity systems work in modern enterprises and consumer applications — authentication factors, federation protocols (OAuth 2.0, OIDC, SAML), authorization models (RBAC, ABAC), privileged access management, and identity lifecycle — with practical guidance for designing and operating identity-centric security.
Associate

Network Security Basics
The Network Security Basics course teaches how to defend networks against common threats — perimeter and internal segmentation, firewalls, IDS/IPS, secure protocols, VPNs, wireless security, and DDoS mitigation — with practical guidance for designing and operating defensible networks.

Threat Modeling Basics
The Threat Modeling Basics course teaches structured approaches to identifying and mitigating threats during system design. Learners practice STRIDE, attack trees, data flow diagrams, and lightweight modern frameworks (Shostack's four-question framework, MITRE ATT&CK), and produce concrete mitigations for realistic systems.

Zero Trust Concepts
The Zero Trust Concepts course teaches the principles, architecture, and pragmatic adoption patterns of zero trust — from 'never trust, always verify' through identity-centric access, microsegmentation, ZTNA, and continuous verification — with cross-references to NIST SP 800-207, BeyondCorp, and modern policy engines.
Why AccelaStudy® AI
40-60% Less Study Time
Skip what you know. Target what you don't.
Score Prediction
Know your pass probability before booking the exam.
Cross-Domain Transfer
Knowledge transfers automatically between related domains.
Start studying Security today
Adaptive learning that skips what you know and targets what you don't.
Create Free Account